-
Gallery of Images:
.jpg)
-
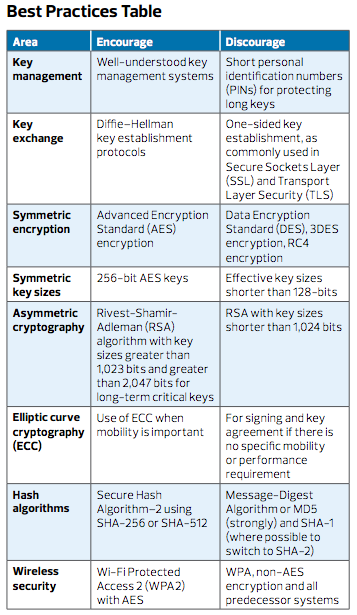
Network security projects. Network security Projects consists of the provisions and policies adopted by a network administrator to prevent and monitor unauthorized access, modification, misuse of a computer network. The art of using maths to encrypt and decrypt data is known as cryptography. One can save confidential information or transfer it through various insecure networks that no one. Tom Dunigan's Security Page: An excellent list of pointers to cryptography and network security web sites. Helgar Lipma's Cryptology Pointers: Another excellent list of pointers to cryptography and network security web sites. Cryptography I from Stanford University. Cryptography is an indispensable tool for protecting information in computer systems. In this course you will learn the inner workings of cryptographic systems and how to correctly use them in realworld. Book Review: This book is appropriate for students studying cryptography and computer security and the graduate and undergraduate level. The author presents a practical survey of the principles and practice of cryptography and network security. Notice This lecture note (Cryptography and Network Security) is prepared by XiangYang Li. This lecture note has benefited from numerous textbooks and online materials. Cryptography and network security 1. CRYPTOGRAPHY PRATIKSHA PATIL 2. CONTENTS o Introduction o Need of Cryptography o Types of Attacks o Techniques of Cryptography o Encryption Algorithm Symmetric Asymmetric o Digital Signature o Visual cryptography For onesemester, undergraduate or graduatelevel courses in Cryptography, Computer Security, and Network Security. In this age of viruses and hackers, of electronic eavesdropping and electronic fraud, security is paramount. As the disciplines of cryptography and network security have matured, more. For onesemester, undergraduate or graduatelevel courses in Cryptography, Computer Security, and Network Security. In this age of viruses and hackers, of electronic eavesdropping and electronic fraud, security is paramount. As the disciplines of cryptography and network security have matured, more practical, readily available applications to enforce network security have developed. CRYPTOGRAPHY AND NETWORK SECURITY LECTURE NOTES for Bachelor of Technology in Computer Science and Engineering Information Technology Department of Computer Science and Engineering Information Cryptography and Network Security. For onesemester, undergraduate or graduatelevel courses in Cryptography, Computer Security, and Network Security. The book is suitable for selfstudy and so provides a solid and uptodate tutorial. Theory related to cryptography and network security by rrs1988 in cryptography Watch videoUnderstand the basics of cryptography to keep your networks, systems, and data secure. Cryptography and Network Security, Fourth Edition, william stallings PPT Slides Cryptography and Network Security Text: Cryptography and Network Security, Fourth Edition, william stallings As we enter the age of universal electronic connectivity in which viruses, hackers, electronic eavesdropping, and electronic fraud can threaten the prosperity and productivity of corporations and individuals, security is increasingly important. Fortunately, the disciplines of cryptography and network security have matured, leading to the development of practical, available applications to. Since online security threats evolve so quickly, there are dozens of different schools of thought on how best to use encryption to enhance network security not just for. Cryptography and Network Security Forouzan Copy. Cryptography and Network Security Forouzan Copy. Microsoft security, privacy, and cryptography efforts are guided by the responsibility to build and maintain trust in the computing ecosystem with stateoftheart systems, controls, and services. In this video tutorial we study the basic principles of Network security and also see the concept of Cryptography by understanding a basic example. Principle Cryptography and Network Security (Video) Introduction; Modules Lectures. Cryptography and Network Security. Introduction; Overview on Modern Cryptography; An Introduction to Elliptic Curve Cryptography; Application of Elliptic Curves to Cryptography; Implementation of Elliptic Curve Cryptography; Secret Sharing Schemes. The Principles and Practice of Cryptography and Network Security Stallings' Cryptography and Network Security, Seventh Edition, introduces the reader to the compelling and evolving field of cryptography and network security. In an age of viruses and hackers, electronic eavesdropping, and electronic fraud on a global scale, security is paramount. Stallings Cryptography and Network Security, Seventh Edition, introduces the reader to the compelling and evolving field of cryptography and network security. In an age of viruses and hackers, electronic eavesdropping, and electronic fraud on a global scale, security is paramount. The purpose of this book is to provide a practical survey of. Cryptography And Network Security, CNS Notes For exam preparations, pdf free download Classroom notes, Engineering exam notes, previous year questions for Engineering, PDF free download A brief discussion of network security and an introduction to cryptography. We end the presentation with a discussion of the RSA algorithm, and show how it wo Stallings Cryptography and Network Security, Seventh Edition, introduces students to the compelling and evolving field of cryptography and network security. In an age of viruses and hackers, electronic eavesdropping, and electronic fraud on a global scale, security is paramount. Feedback for Cryptography and Network Security Dear student We are glad that you have attended the NPTEL online certification course. We hope you found the NPTEL Online course useful and have started using NPTEL extensively. Cryptography and Network Security Facebook. About the course The aim of this course is to introduce the student to the areas of cryptography and cryptanalysis. This course develops a basic understanding of the algorithms used to protect users online and to understand some of the design choices behind. and network professionals can use cryptography to maintain the privacy of computer data. Starting with the origins of cryptography, it moves on to explain cryptosystems, various Security Services of Cryptography The primary objective of using cryptography is to provide the following four fundamental Cryptography and Network Security Example of a 3x3 matrix Hill Cipher Encryption GATE CSE by Unacademy GATE Preparation. Join Lisa Bock for an indepth discussion in this video, Welcome, part of Learning Cryptography and Network Security. Download Cryptography and network security PDF tutorial by Chandraskhar Rao intended to Bachelor of Technology in Computer Science and Engineering. CRYPTOGRAPHY AND NETWORK SECURITY PRINCIPLES AND PRACTICE FIFTH EDITION William Stallings Prentice Hall Boston Columbus Indianapolis New York San Francisco Upper. Cryptography and Network Security for the Internet Cryptography is the process of making information secret by converting data or text to a coded format to be sent to intended users. The recipient then deciphers the code to obtain the message. For onesemester, undergraduate or graduatelevel courses in Cryptography, Computer Security, and Network Security. The book is suitable for selfstudy an Cryptography and Network Security has 116 ratings and 6 reviews. Derek said: A good introductory book on cryptography and network security related topics This book elaborates the basic and advanced concepts of cryptography and network security issues. It is user friendly since each chapter is modelled with several case studies and illustration. All Selection from Cryptography and Network Security [Book Our 1000 Cryptography and Network Security questions and answers focuses on all areas of Cryptography and Network Security covering 100 topics. These topics are chosen from a collection of most authoritative and best reference books on Cryptography and Network Security. This tutorial covers the basics of the science of cryptography. It explains how programmers and network professionals can use cryptography to maintain the privacy of computer data. Starting with the origins of cryptography, it moves on to explain cryptosystems, various traditional and modern ciphers. SLogix offers Best Projects in Network Security and Cryptography, Network Security Projects in Java, BE Network Security Projects, Best Network Security Projects Cryptography Network Security (McGrawHill Forouzan Networking) [Behrouz A. FREE shipping on qualifying offers. A textbook for beginners in security. In this new first edition, wellknown author Behrouz Forouzan uses his accessible writing style and visual approach to simplify the difficult concepts of cryptography and network security. CRYPTOGRAPHY AND NETWORK SECURITY Free download as Word Doc (. Cryptography is a method of storing and transmitting data in a particular form so that only those for whom it is intended can read and process it. The term is most often associated with scrambling plaintext (ordinary text, sometimes referred to as cleartext) into ciphertext (a process called encryption), then back again (known as decryption). In computing, Network Security Services (NSS) NSS provides security tools required for debugging, diagnostics, certificate and key management, cryptographymodule management, and other development tasks. NSS comes with an extensive and growing set of documentation. Cryptography and Network Security. Cryptography historically dealt with the construction and analysis of protocols that would prevent any third parties from reading a private communication between two parties. William Stallings' Cryptography and Network Security: Principles and Practice, 5e is a practical survey of cryptography and network security with unmatched CRYPTOGRAPHY, NETWORK SECURITY AND CYBER LAW [As per Choice Based Credit System (CBCS) scheme (Effective from the academic year 2016 2017) A tutorial and survey covering both cryptography and network security protocols and technology. Each of the basic topics of cryptography, including conventional and publickey cryptography, authentication, and digital signatures, are covered. Cryptography and Network Security has 374 ratings and 22 reviews. Lucy said: The edition I had was probably a bit out of date but it was readable and fai.
-
Related Images: